Site Contents
Related News
Last updated: 2026-03-25 06:41
-
This Microsoft security team stress-tests AI for its worst-case scenarios - Fast Company
2026-03-24 20:10 www.fastcompany.com -
AI agent discovery: Inventory and govern shadow AI agents | Nudge Security
2026-03-24 17:43 securityboulevard.com -
Cybersecurity's new race: Finding the CrowdStrike or Wiz of AI security - Axios
2026-03-24 17:36 www.axios.com -
Modernizing U.S. Critical Infrastructure for the AI Era: Strengthening Security In an Evolving ...
2026-03-24 17:25 blogs.cisco.com -
RSA 2026 Exposes Security Gaps as AI Factories and GPU Blind Spots Dominate Risk
2026-03-24 17:12 futurumgroup.com -
New Omnissa 2026 Study Finds Shadow AI, Security Gaps, and Device Instability Expose ...
2026-03-24 16:26 www.01net.it -
Phantom Labs analysis of BeyondTrust's Identity Security Insights Data finds enterprise AI ...
2026-03-24 16:22 www.intelligentciso.com -
Absolute Security Announces Agentic AI Cyber Resilience Innovations to Help Global ...
2026-03-24 16:08 lasvegassun.com -
News: AI-native Security Assurance leads the GRC Transformation
2026-03-24 15:26 securityboulevard.com -
Cyberhaven Closes the AI Security Gap Amid the Meteoric Rise of Agentic AI - PR Newswire
2026-03-24 15:04 www.prnewswire.com -
99% of Organizations Were Hit by a SaaS or AI Ecosystem Security Incident in 2025 ...
2026-03-24 14:14 aithority.com -
Pressure to adopt AI has led to critical security gaps for enterprises | Biometric Update
2026-03-23 19:52 www.biometricupdate.com -
Cisco goes all in on agentic AI security | Network World
2026-03-23 19:28 www.networkworld.com -
AccuKnox Launches AI-Security 2.0 to Extend Zero Trust Protection to AI Models and Agents
2026-03-23 18:15 securityboulevard.com -
Datadog Launches AI Security Agent to Combat Machine-Speed Cyberattacks
2026-03-23 18:14 securityboulevard.com -
Cisco Reimagines Security for the Agentic Workforce - PR Newswire
2026-03-23 18:00 www.prnewswire.com -
AnyInsight.ai Introduces Industry-first AI Firewall Platform for Enterprise AI Security at RSA ...
2026-03-23 17:10 www.knoxnews.com -
X-PHY Deepfake Detector Wins Global InfoSec Award for Innovative AI Security and Safety ...
2026-03-23 16:12 en.prnasia.com -
Top 10 Security Risks in AI Agents Explained - YouTube
2026-03-23 15:39 www.youtube.com -
Google Cloud expands its AI security capabilities through Wiz integration - Techzine Europe
2026-03-23 15:20 www.techzine.eu
* This information has been collected using Google Alerts based on keywords set by our website. These data are obtained from third-party websites and content, and we do not have any involvement with or responsibility for their content.
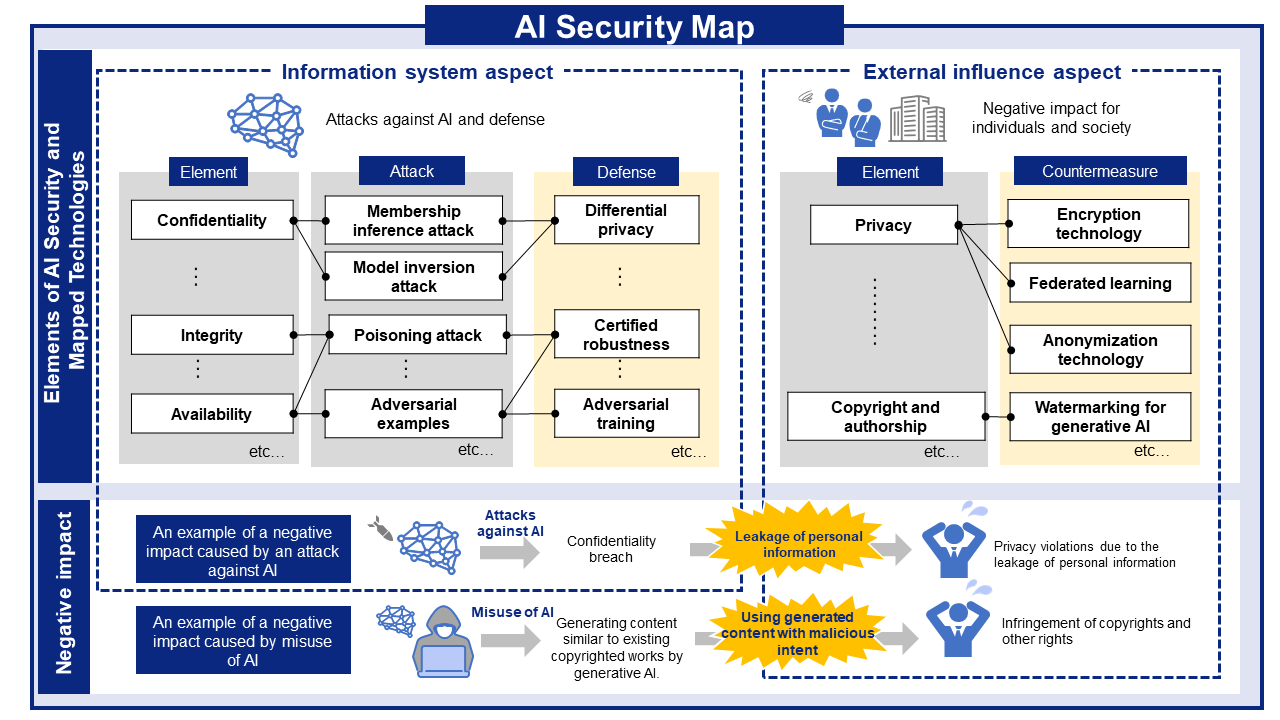
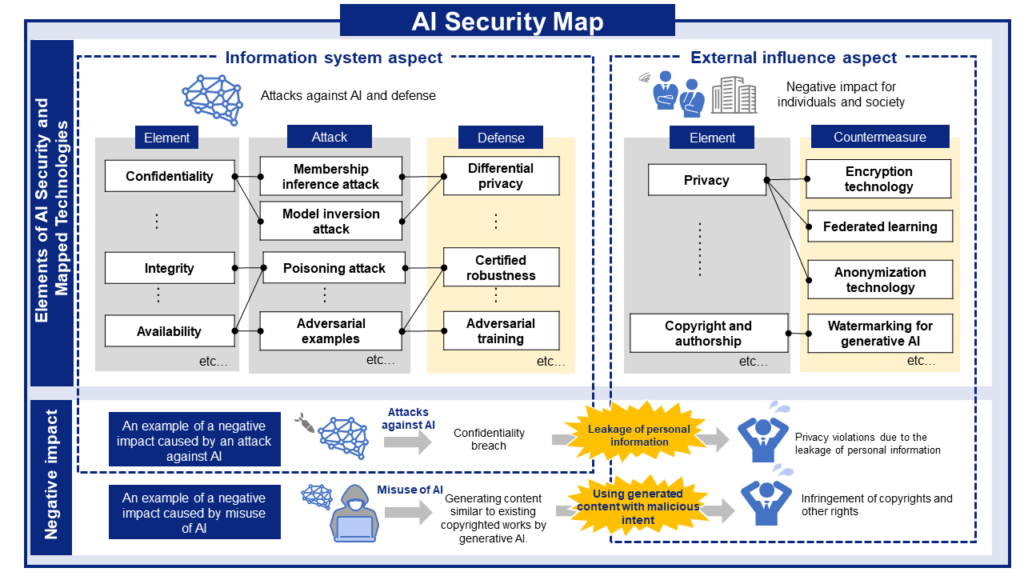
AI Risks, Impacts, and Mitigations at a Glance
AI security threats and related mitigations, organized from two perspectives: information Systems and People and Society.
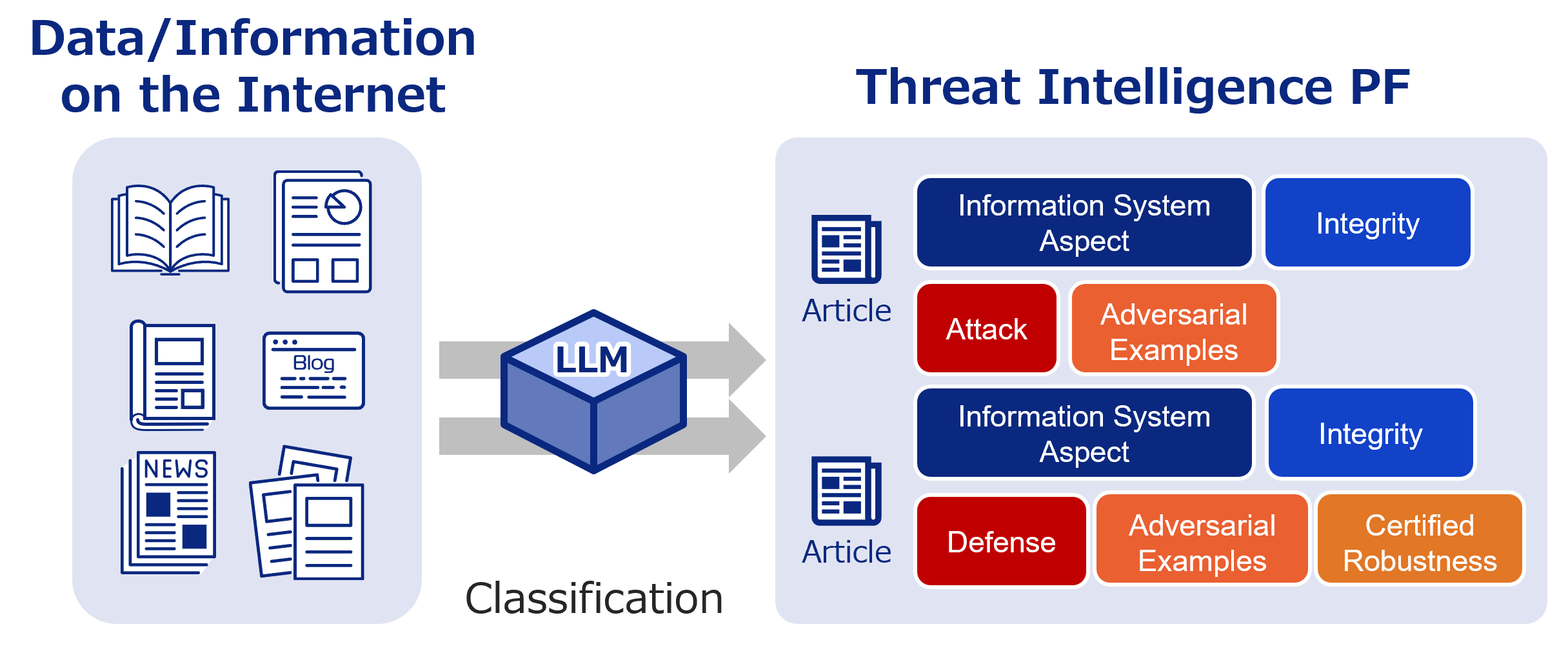
AI Security Information Gathering and Research
Labeled bibliographic information. Use it to research the latest trends and more.
Recent literature

Evaluating the Reliability and Fidelity of Automated Judgment Systems of Large Language Models
Authors: Tom Biskupski, Stephan Kleber | Published: 2026-03-23
2026.03.232026.03.25

SecureBreak — A dataset towards safe and secure models
Authors: Marco Arazzi, Vignesh Kumar Kembu, Antonino Nocera | Published: 2026-03-23
2026.03.232026.03.25

Structured Visual Narratives Undermine Safety Alignment in Multimodal Large Language Models
Authors: Rui Yang Tan, Yujia Hu, Roy Ka-Wei Lee | Published: 2026-03-23
2026.03.232026.03.25

-scaled.png)