Site Contents
Related News
Last updated: 2026-03-19 06:42
-
Claude Code Security and Magecart: Getting the Threat Model Right - The Hacker News
2026-03-18 17:03 thehackernews.com -
Tufin introduces AI agents to take on network security work - Help Net Security
2026-03-18 16:51 www.helpnetsecurity.com -
Exclusive: AI cybersecurity startup RunSybil raises $40 million in round led by Khosla Ventures
2026-03-18 15:48 fortune.com -
Graylog advances explainable AI and automated workflows for faster threat detection
2026-03-18 15:32 www.helpnetsecurity.com -
StrongestLayer offers AI-native email security detection & automated risk investigation
2026-03-18 15:03 www.computerweekly.com -
Nvidia details NemoClaw security guardrails in wake of AI agent concerns - SDxCentral
2026-03-18 14:57 www.sdxcentral.com -
PointGuard AI Unveils MCP Security Gateway to Secure Autonomous AI Agents
2026-03-18 14:36 www.jsonline.com -
CrowdStrike Innovates to Modernize National Security and Protect Critical Systems
2026-03-18 14:35 www.crowdstrike.com -
#ai #security #aiagents #ad #vantapartner | Steve Nouri | 20 comments - LinkedIn
2026-03-18 14:27 www.linkedin.com -
1Password introduces Unified Access platform and partner API for AI agent security
2026-03-17 19:01 siliconangle.com -
RSAC 2026 Innovation Sandbox | Geordie AI: Architect of Enterprise AI Agent Security ...
2026-03-17 18:49 securityboulevard.com -
VSBLTY And Burkhan World Announce Strategic Partnership To Accelerate AI Security And ...
2026-03-17 18:34 www.thenewswire.com -
Cato Networks rolls out Neural Edge and AI Security to protect enterprise AI workloads
2026-03-17 18:31 siliconangle.com -
Cato Brings GPUs Into SASE to Tackle AI Security at Scale | news - ChannelE2E
2026-03-17 17:01 www.channele2e.com -
National cyber director expands on Trump administration's vision for AI security, industry ...
2026-03-17 16:09 www.cybersecuritydive.com -
New investments in AI-powered open source security - Google Blog
2026-03-17 16:08 blog.google -
AI amplifying fraud at 'staggering' rate, security watchers warn | National Post
2026-03-17 15:33 nationalpost.com -
VSBLTY And Burkhan World Announce Strategic Partnership To Accelerate AI Security And ...
2026-03-17 14:26 www.tradingview.com -
Virtue AI Closes the AI Agent Security Gap with Agent ForgingGround: The First Enterprise ...
2026-03-17 14:22 aithority.com -
Securing Enterprise Agents with NVIDIA OpenShell and Cisco AI Defense
2026-03-16 20:35 blogs.cisco.com
* This information has been collected using Google Alerts based on keywords set by our website. These data are obtained from third-party websites and content, and we do not have any involvement with or responsibility for their content.
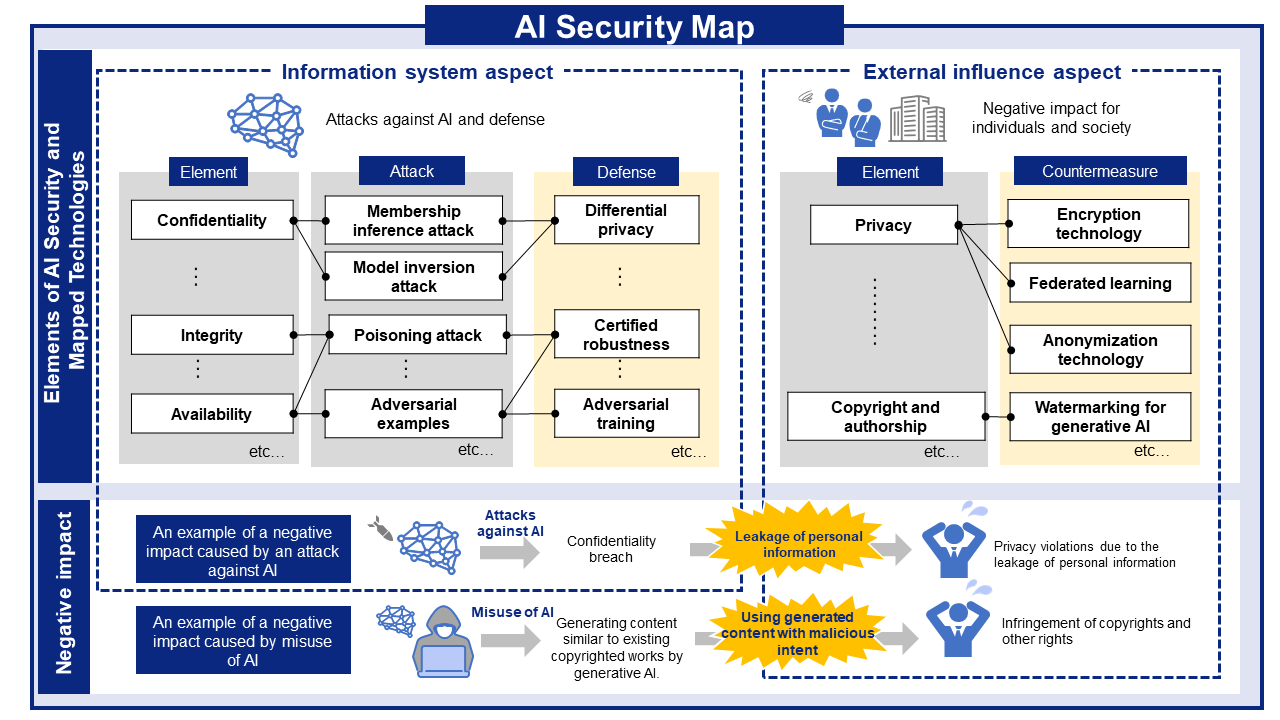
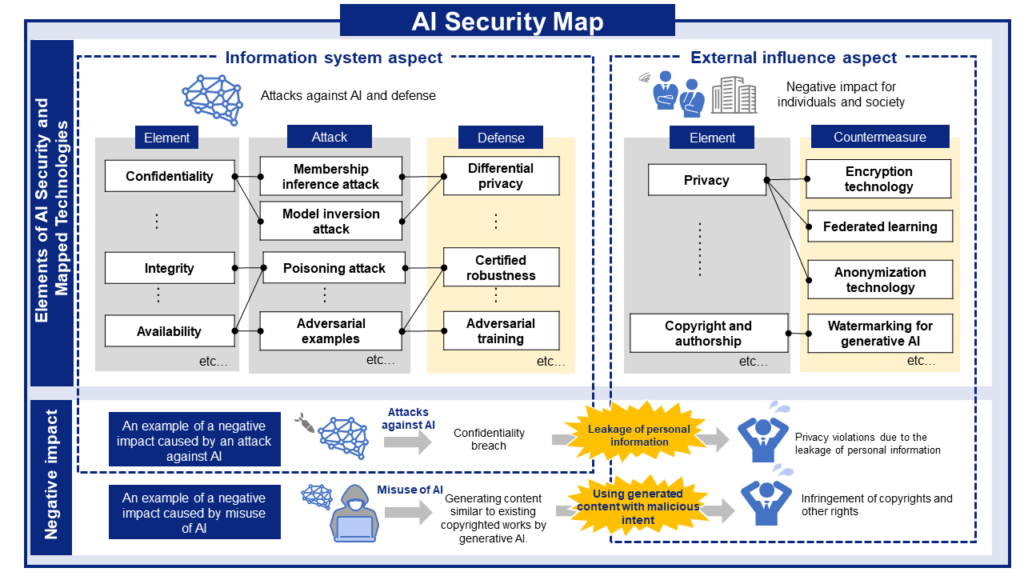
AI Risks, Impacts, and Mitigations at a Glance
AI security threats and related mitigations, organized from two perspectives: information Systems and People and Society.
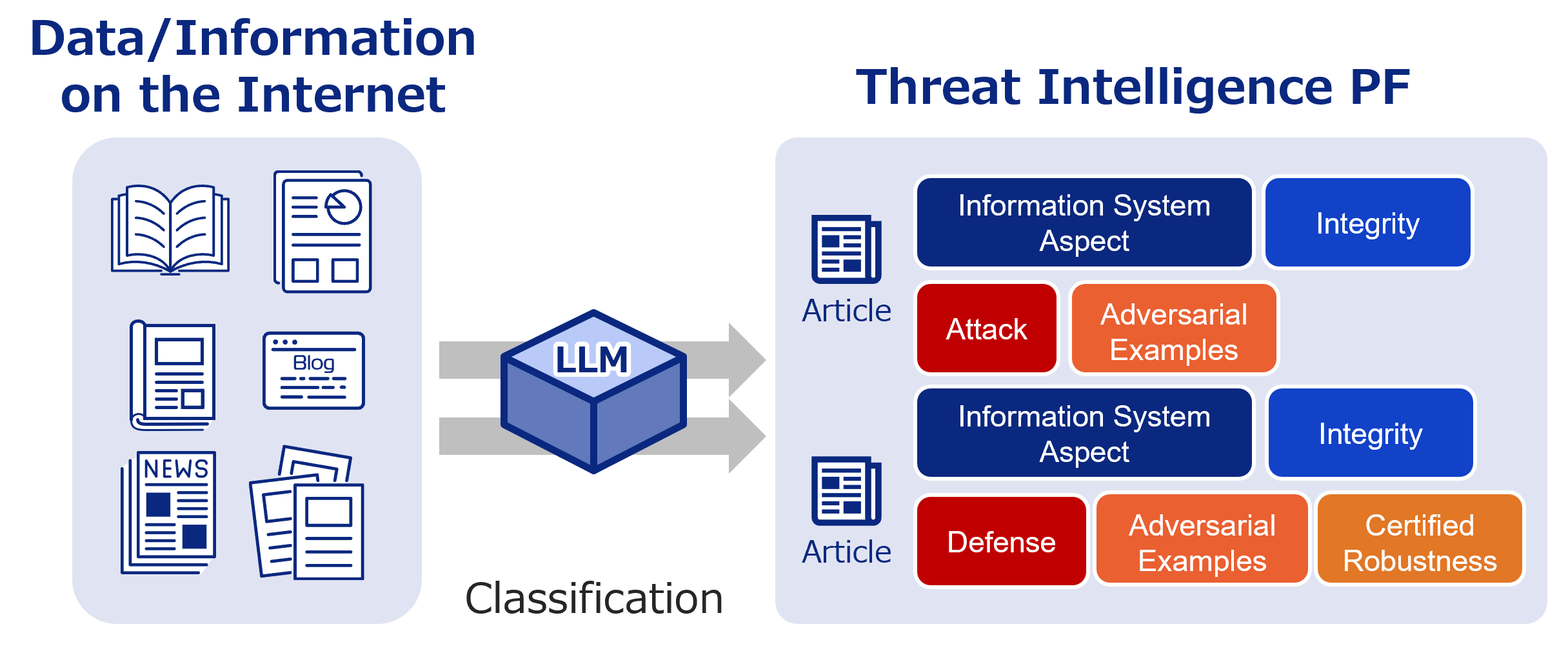
AI Security Information Gathering and Research
Labeled bibliographic information. Use it to research the latest trends and more.
Recent literature

SAMSEM — A Generic and Scalable Approach for IC Metal Line Segmentation
Authors: Christian Gehrmann, Jonas Ricker, Simon Damm, Deruo Cheng, Julian Speith, Yiqiong Shi, Asja Fischer, Christof Paar | Published: 2026-03-17
2026.03.172026.03.19

Rotated Robustness: A Training-Free Defense against Bit-Flip Attacks on Large Language Models
Authors: Deng Liu, Song Chen | Published: 2026-03-17
2026.03.172026.03.19

Resource Consumption Threats in Large Language Models
Authors: Yuanhe Zhang, Xinyue Wang, Zhican Chen, Weiliu Wang, Zilu Zhang, Zhengshuo Gong, Zhenhong Zhou, Li Sun, Yang Liu, Sen Su | Published: 2026-03-17
2026.03.172026.03.19

-scaled.png)